Current State Security Assessment (CSSA)
How we can help
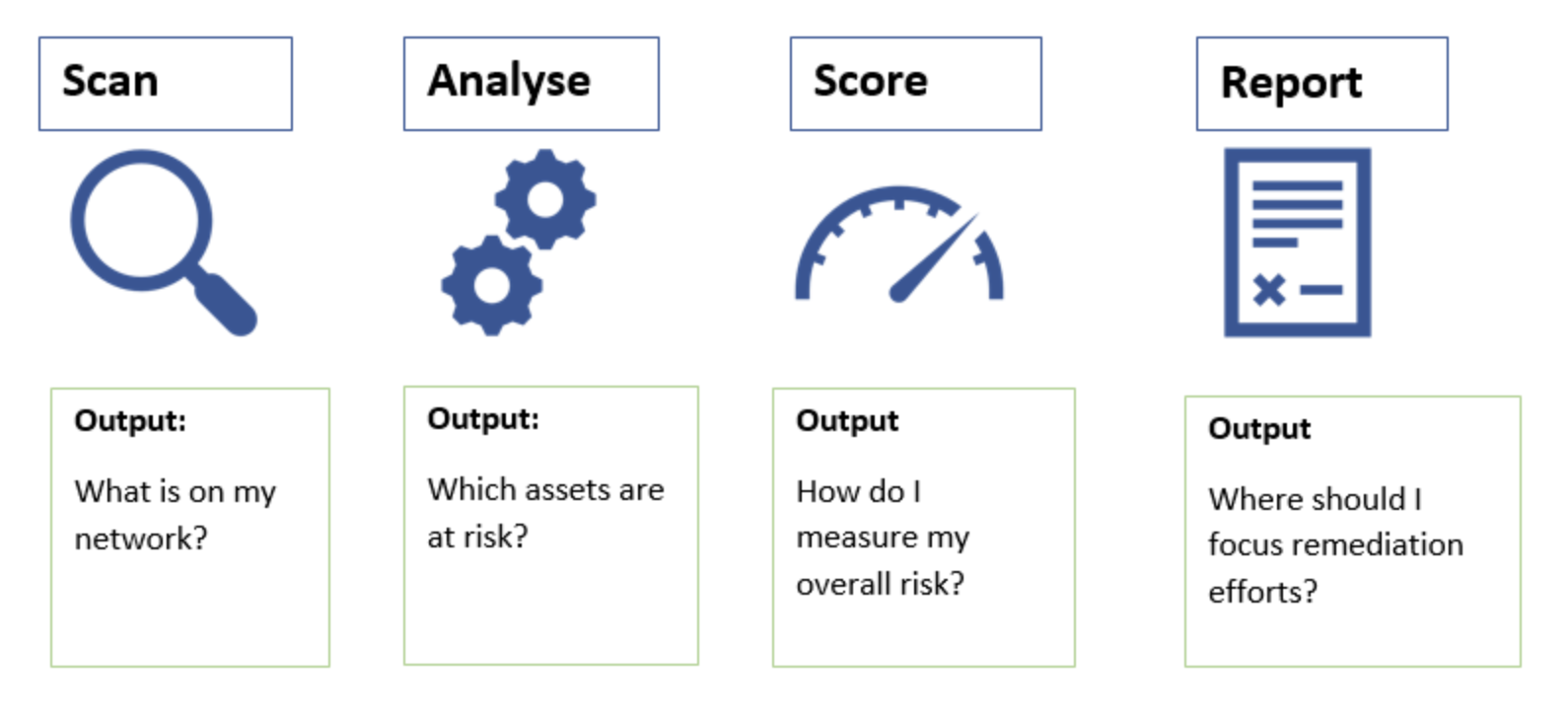
With vulnerabilities, seeing is believing. Current State Security Assessment (CSSA) takes the guesswork out of the way businesses and IT management respond to “How safe are we?” .
Accuracy in security assessment is the primary requirement but if it isn’t there then little else matters.
What separates our CSSA from run of the mill scanning is -in a word – accuracy, leading to establishing a cybersecurity maturity score and an independent jargon-free cyber report for the Board of Directors, CIOs and/or insurance companies as required.
We use time-tested practical approaches and widely deployed industry tools for identifying the vulnerabilities, configuration issues and risks that an attacker could use as an opportunity for exploitation. We ensure the visibility we create will help you shrink the attack surface and eliminate attack vectors in your organisation.
How we do it
We start with a breadth of assessments that review processes, documentation as well as existing technology solutions to create visibility on your point-in-time vulnerabilities for traditional IT assets (laptops, desktops, on-premise servers).
These assessments include:
- Credential scanning
- Policy audit
- Network and host scanning
Once the intricacies of your organisation’s ICT infrastructure have been mapped out and access rights authorized, we proceed to deploy the scanning tool into your environment to illuminate potential vulnerabilities and provide prioritized risk-based recommendations to improve your security posture against:
- A defined security standard e.g. ISO 27001:2013 controls
- Security “baseline”
- Internal policy
Benefits to You
It’s time your IT delivered results
Have an IT specialist call you to discuss your technology needs.